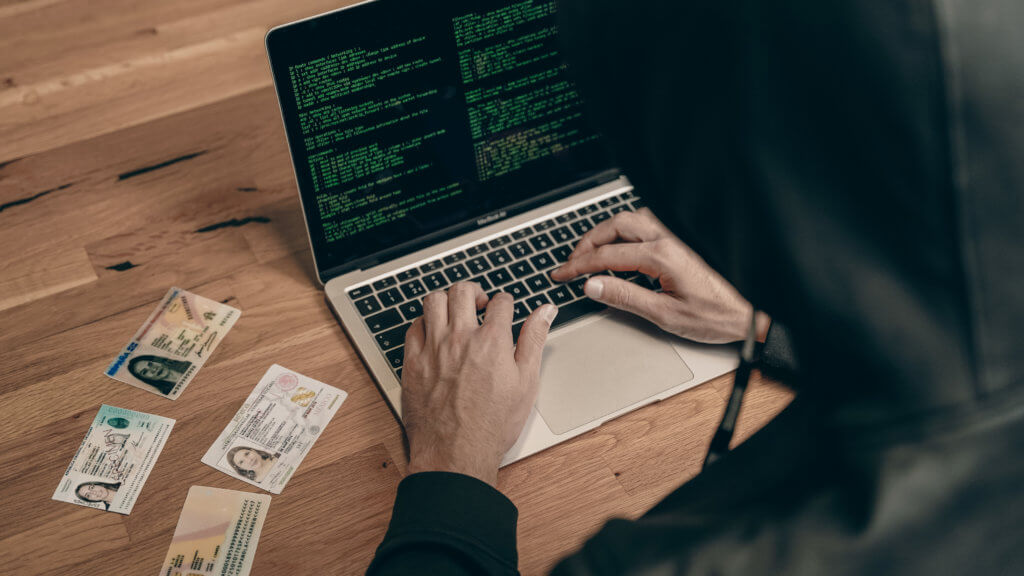
The Problem of Synthetic Shopper: Actionable eCommerce Fraud Prevention Tactics
Over 54% of companies say that they’ve experienced a cyberattack within the previous year of their operation. Fraudsters are constantly coming up with different ways to bypass previously established security measures.
One such type of fraud is the synthetic shopper, which deals with identity theft to hurt businesses severely. Businesses need to be on their feet if they want to combat different types of identity theft and protect themselves in the long run.
In this guest post, we take an in-depth look at synthetic fraud and actionable eCommerce fraud prevention tactics to help you stay one step ahead of fraudsters at all times.
The Problem of Synthetic Shoppers: Actionable eCommerce Fraud Prevention Tactics
The origin of the concept of cyber security can be traced back to the 1970s. Back then, the more common cyber threats were viruses and security breaches. Today, the nature of online threats has become far more personal and malicious.
Some of the most common cyber threats faced by companies today are:
- DDoS attacks
- Malware
- Phishing
- Botnets
- Corporate account takeovers
While some attacks are aimed at the disruption of the service provided by the business, some aim to manipulate the identity of the company in order to scam them and their customers.
Synthetic identity theft is one such fraud that involves the manipulation of identities with the help of fake and generated data. It causes heavy losses to companies and is challenging to detect.
Let’s take a look at how eCommerce businesses can protect themselves against this sly threat with actionable strategies.
Understanding the intricacies of synthetic identity fraud
The first step in preventing synthetic identity fraud is understanding the intricacies of this crime. This is important because when the fraud involves the manipulation of something so fundamental as identities, it's quite challenging to detect.
Many businesses fail to detect it because they don't understand it or know about it enough to set parameters of identification. Here is a detailed guide on what synthetic identity fraud is, highlighting its process and magnitude of impact.
Put simply, synthetic identity theft refers to combining real and fake identity information to create accounts and make purchases with a business. It causes businesses massive damage because the purchases are not authentic, resulting in chargebacks and other losses.
This in turn results in the goodwill of a business suffering. Shoppers are already wary of buying from new business sites, so acquiring a large number of chargebacks will only damage your reputation and make it even harder to acquire genuine shoppers.
Types
Synthetic identity theft can be categorized into three major types of fraud:
- i) Manipulated synthetic theft — This refers to combining genuine user documents with fake data in order to appear as a real person and engage with a business. The real information allows the fraudulent account to showcase authenticity and bypass typical security measures.
- ii) Blended synthetic theft — This process sees fraudsters combining real information from multiple sources to pose as an entirely new person. Because this method uses 100% authentic information, it becomes hard to detect them.
- iii) Manufactured synthetic theft — This method used entirely fake information but one that may seem real. For instance, a fraudster may use a random social security number to fall within the right range. It’s fake but can bypass the security measure because it’s made to appear authentic.
Process
Understanding the process used by fraudulent people will help you put better identification markers on every step and secure your business more efficiently. While the process used by scammers when recreating a synthetic identity theft can vary depending on various factors, they usually use the following template:
- The scammer collects personal information either through stealing or purchasing it off the dark web.
- They create an identity by combining real and fake information.
- They use this resulting identity to engage with a business, such as by purchasing items off a website on credit.
- They will pay their dues for a while to appear legitimate.
- After some time, they will purchase an expensive item on credit.
- They disappear and leave the business with no trail to follow because the customer wasn't authentic.
Impact on a Business
Synthetic identification theft has been reported as the fastest-growing financial crime by the 2021 Future of Fraud Forecast. The Federal Trade Commission (FTC) received reports of 1.4 million identity theft cases in 2023 alone (up to the time of this writing). The most valuable aspect this kind of fraud damages for a business is its goodwill.
Here are the different ways a business can suffer from identification theft:
- Credit card fraud
- Chargebacks:
Unpaid loans taken out in your name
- Lowered credit score
- Potential legal action against you
Review your Current Security Measures
To combat identity theft, it’s important to take into account the current framework, structure, and operations of your business. Review them to identify weak points where leaks can occur.
Fraudsters are able to commit theft when they get their hands on your confidential information, which they use to breach your security protocol and enter your system. Identifying where and how leaks happen will make you instill better security measures for tighter security.
For most eCommerce companies, the following are the most common thefts that jeopardize their identity data:
- Data leaks — Your information that is held or protected by a third party is leaked online.
- Account takeovers — Someone infiltrates one of your online accounts to mine it for personal information.
- Phishing — Someone tricks you into revealing personal information, such as your date of birth, login name, and password.
- Cyberattack — A malicious software attacks your system and steals personal information held in there.
See what types of attacks your business has been suffering through in the past. Identify weak spots and consider how you can eliminate or strengthen them.
For example, if you suffer from data leaks, consider the possibility that some employees are involved. Review their interactions with third parties to see if the leaks are happening there.
Instill Sturdy Security Measures
Once you have a general idea of your security framework, work to strengthen it to prevent identity data breaches and theft. Some common measures you may undertake in this regard are listed below:
- Password-protect everything — Have the option of using password protection on as many information files as you can. Pick passwords that are unique and complex. Only give out passwords to a limited number of people. Change passwords from time to time.
- Restrict interaction with third parties — Only indulge with third parties as necessary. Make sure their presence is removed from your system as soon as your association with them ends. This means that if a third party needs to be consulted after two months, remove them from the system until that time.
- Use fraud prevention tools — Tools such as antivirus software solutions, 2FA, encryption, and verification systems are simple measures that identify suspicious activities and report them to you immediately.
- Review credit reports — Suspicious financial activity is one of the earliest signs of identity theft. Check your credit reports on a regular basis and compare them to both previous reports and your expected forecast for them.
- Use device fingerprinting — This module identifies the tools that scammers use to appear as different, unrelated users. It identifies repeating elements such as proxy usage, suspicious browser setups, and unusual hardware configurations.
- Use digital footprint analysis — A digital footprint analysis software looks up email addresses, phone numbers, and the social platforms used by a digital visitor to verify their legitimacy. If their digital footprint doesn't appear to be legitimate, they will be flagged for further investigation.
- Study the behavior of users — As scammers deploy more and more tools to mimic human behavior as closely as possible, it becomes increasingly important to make efficient differentiation between them. This includes observing factors such as the speed of their browsing and the pattern of cursor movements.

Train your Employees
One of the lesser-discussed aspects of fool proofing your business against identity theft is to train your employees in that regard. Training your employees to understand what identity theft is as well as how they can identify it will go a long way in protecting your business.
Employees are the ones who undertake both large and small operations of your eCommerce business. When they’re armed with valuable knowledge about identifying and preventing theft, your workers can identify and nullify such attempts as soon as they come in contact with your employees.
Conduct training camps for each and every employee to train them about identity theft. Give them handy guides to refer to whenever they need to. Finally, encourage them to speak up against identity theft as soon as they detect it.
Identify Theft Right at the Gate to Secure your Business
Identity theft is one of the fastest-growing cyber threats that affect a large number of small businesses.
As an eCommerce business, you should strive to protect yourself against it by deploying the right safety measures.
Begin by gaining a thorough understanding of how the theft is conducted to target those elements for better security. Review your current safety framework to deploy efficient safety measures. Last of all, train your employees to identify and fight against identity crime efficiently.
Let us know in the comments what you think are the most efficient ways to combat identity theft as an eCommerce company! Contact our team at BlueTuskr, an e-commerce marketing agency, if you have any questions.
Author Bio
Atreyee Chowdhury is a freelance content writer with more than 10+ years of professional experience. She’s passionate about helping SMBs and enterprises achieve their content marketing goals with her carefully crafted and compelling content. She loves to read, travel, and experiment with different cuisines in her free time. You can follow her on LinkedIn.
Connect With Us
Recent Post
- May 07, 2026
- Author: Andrew Maff
Google Shopping Ads: Best Practices for Scalable E-Commerce Growth
- Apr 30, 2026
- Author: Andrew Maff
How to Increase Average Order Value Without Hurting Conversion Rate
- Apr 21, 2026
- Author: Andrew Maff
Customer Lifetime Value for E-Commerce Brands: What Actually Drives It

.png)




%20(1).jpg)



Tell us what you think!